Dear BestHacking readers today I am going to tell you How to Remove a Virus Using Command Prompt
Virus is a computer program that can copy itself and infect your computer. These viruses can spread via USB/flash drive or from one computer to other computer by few written codes. There are many antivirus software available to remove viruses from computer. But there are some viruses or suspicious files which can’t be removed by any antivirus software. Some suspicious files such as autorun.inf initiate all the viruses in pc. These files must be removed for safe operation of your pc, because they may lead to data loss, software damages etc. Such viruses and files can be removed by using cmd. In this article we will discuss how to remove a virus using command prompt.
Tricks These Days
Friday, 30 May 2014
Thursday, 29 May 2014
Downloading Torrent Using Internet Download Manager
Hello friends, today i will show you the way to download torrents with Internet Download Manager. Torrent is tiny file with .torrent extension which allows you to download huge amount of data. We use torrents to download various stuffs like movies, games, software package and plenty of different things. you'll transfer torrents from several website. The transfer speed for torrents depends on seeds it has. It will make difficult for you to download files with very low or no seed counts. However with the assistance of this trick you'll be able to download torrent file with IDM. This tool can be really helpfull when you want to download file that has very low seeds. IDM is the quickest file transfer manager on the internet market. So lets begin!
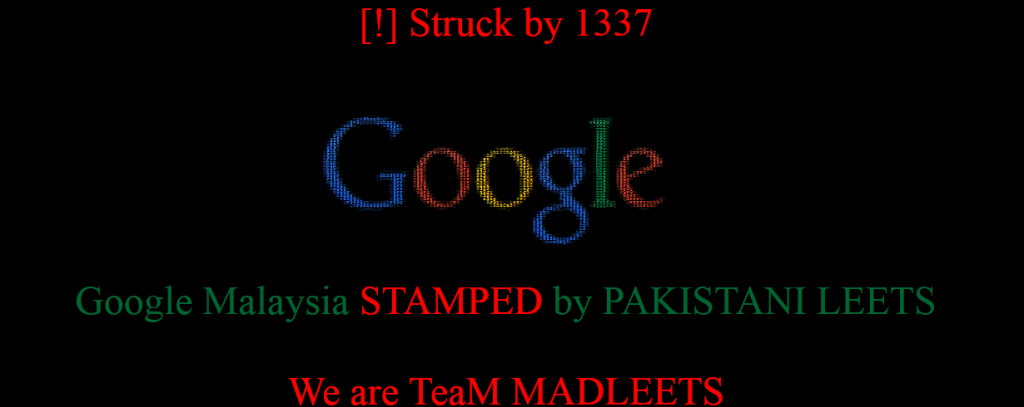
Google Malaysia gets Hacked by 1337 Hacker
The NIC hacker hit domain registrar again and this time 1337 hacker hijack Google Malaysia official domains(www.google.com.my) with DNS poisoning attack. At the time of writing, Both of Google Malaysia official sites are defaced and showing the message left by the hackers.
Wednesday, 28 May 2014
How facebook Hacking can be done ? 7 Methods
These days Everyone is complaining about his / her Facebook account being hacked and he/she wants to Recover it. It has become quite big problem now a days Because of Poor Knowledge on How Stuff works Online. So i thought, i will create one exclusive Post for all the Facebook users out there, Who are so curious to know about Facebook hacking and how their account can be compromised by hackers and Spammers.
Why You Should Learn Programming & Networking
Hi readers, today I'm not gonna share any tutorial or Hack but a short guide, which I've experienced in my learning carrier. Well It's been completely one year! to me in this field (Not Pro, neither Expert!) still a learner. But have you ever thought why experienced Hacker/Researcher always recommend us to learn Programming & Networking before engaging in Hacking ? Well that's what we're supposed to discuss in this post.
Learn Penetration Testing by Web For Pentesters E-book
After a short break! I'm back, Hey wait do you know ? that The Security Layer[www.thesecuritylayer.com] is my new brand blog related to Security and Penetration testing, Do visit you'll love it. Well recently i've found two ebooks for Web For Pentesters, Really it's an amazing, useful, elegant e-book who really wants to learn Penetration Testing and Ethical hacking. Beginner must download and read it.
Dragon City and Monster Legends Hack tools
Hey You often tried to hack you dragon city or monster legends now can can do it yes am providing you dragon city hack and monster legends hackonly in 5$
Subscribe to:
Comments (Atom)